CrowdStrike Falcon Integration
Note: This integration requires Cisco XDR Advantage or Cisco XDR Premier licensing tier.
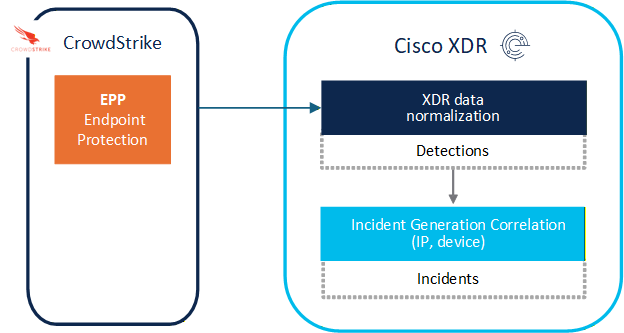
CrowdStrike Falcon is an Extended Detection and Response (XDR) and Endpoint Detection and Response (EDR) offering. CrowdStrike Falcon security events can generate and contribute to correlated incidents in Cisco XDR.
In Cisco XDR, we enable CrowdStrike Falcon users to leverage it for threat hunting and investigation features as well as rapid response actions to understand and defend against threats on the endpoint. It also provides important device inventory context to help triage detected threats.
Use the CrowdStrike Falcon integration to query for security detections of many different observables including file, network, email, host, and process identifiers, as well as to add MD5 and SHA-256 file hashes, IPv4 and IPv6 addresses, and domain names to blocklists, and isolate specific hosts from the network. This integration can also provide host and vulnerability information to Cisco XDR for triaging detections and incidents.
Cisco XDR ingests from CrowdStrike Falcon:
-
Security events: Referred to as Endpoint Detections in the CrowdStrike console.
-
Supporting evidence: Endpoint activities that contributed to the security event, such as file system activities, process activities, and so on.
Ingestion details:
-
Endpoint Detection type: Endpoint Protection (EPP) only.
-
Severity levels: Critical (80-100), High (60-79), Medium (40-59), and Low (20-39). Events with severity values 1–19 are considered Informational and are not ingested.
Cisco XDR does not ingest other types of CrowdStrike security events, such as mobile, CWPP, data protection, IdP, NGSIEM, OverWatch, third-party, and XDR.
-
In the Cisco XDR navigation menu, choose Administration > Integrations.
-
On the Integrations page, click the Third-Party tab and navigate to the CrowdStrike Falcon integration.
-
Click the plus sign (+) in the lower-right corner of the card. The CrowdStrike Falcon integration page is displayed.
-
Expand the Integration Guide area and follow the instructions on how to add the CrowdStrike Falcon integration in Cisco XDR.
Incidents are groups of correlated events generated using data ingested from your integrated products. By correlating events which could be part of a larger threat into an incident, it reduces the time typically required to investigate individual security alerts or detections. For more information about Cisco XDR Incidents feature, see Incidents.
When you enable the Crowdstrike Falcon integration, Cisco XDR ingests the detections and security events that are sent by CrowdStrike Falcon and uses them for incident correlation.
To view incidents with Crowdstrike Falcon data:
-
In the Cisco XDR navigation menu, choose Incidents.
-
Look for Crowdstrike Falcon in the Source column to find incidents generated with Crowdsrike Falcon data.
-
Select an incident and open the Incident Detail page.
-
Click on the Detection page to see events from Crowdstrike Falcon and other sources.
To verify that Cisco XDR is receiving Crowdsrike Falcon data when no incidents are present, go to the Investigate > Detection findings page and filter the table by Crowdsrike Falcon using the Source drop-down list. For more information, see the Detection Findings help topic.
You can perform the following tasks after you integrate CrowdStrike Falcon with Cisco XDR:
-
Investigations Start a new investigation into any combination of file, network, email, host, process identifiers, and file hashes and the results will include any records of them found in CrowdStrike Falcon. To verify that this integration is working, and to see what kind of data is returned, investigate one or more observables about which you know CrowdStrike Falcon has recent information. For details, see Investigate.
-
Detection findings - View the security events generated by CrowdStrike Falcon to validate the data that is ingested by Cisco XDR for incident generation. For details, see Detection Findings.
-
Pivot Menu - Use the Pivot menu to access actions in CrowdStrike Falcon. Available actions include the option to open observables in Crowdstrike Endpoint detections search, and perform actions on indicators, such as allow, block, or detect only. You can also install workflows from the Automation Exchange to add more actions to the Pivot menu.
-
Assets - View devices as reported by CrowdStrike Falcon. For more information, including on how to filter the view to only the reports from CrowdStrike Falcon, see Devices.
-
Automation:
-
Atomic Actions - The atomic actions for CrowdStrike Falcon can be used as building blocks in custom workflows. These can be found as available Actions in the left menu of the Workflow Editor. See Atomic Actions and Workflows.
-
Workflows - The workflows for CrowdStrike Falcon can be installed from the Automation Exchange. See Workflows and Exchange.
-
Target - The CrowdStrike Falcon target is automatically created for out-of-box and custom workflows. See Targets Created From Integrations.
-
Playbooks - An Automation system workflow that uses CrowdStrike Falcon and is included in the Cisco Managed Incident Playbook can be used to Contain Incident: Assets (Devices), Contain Incident: File Hashes, Identify Vulnerabilities, and Validate Eradicated Hosts and Unquarantine Assets. See Containment and Recovery on the Response page.
-